Intelligent, geo-enabled security
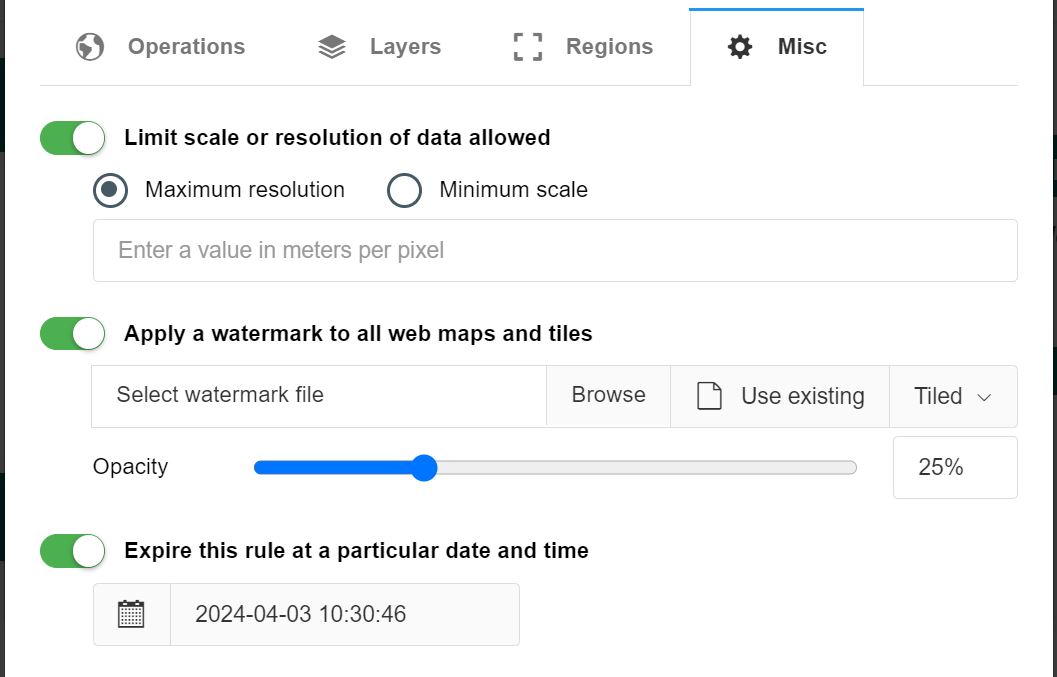
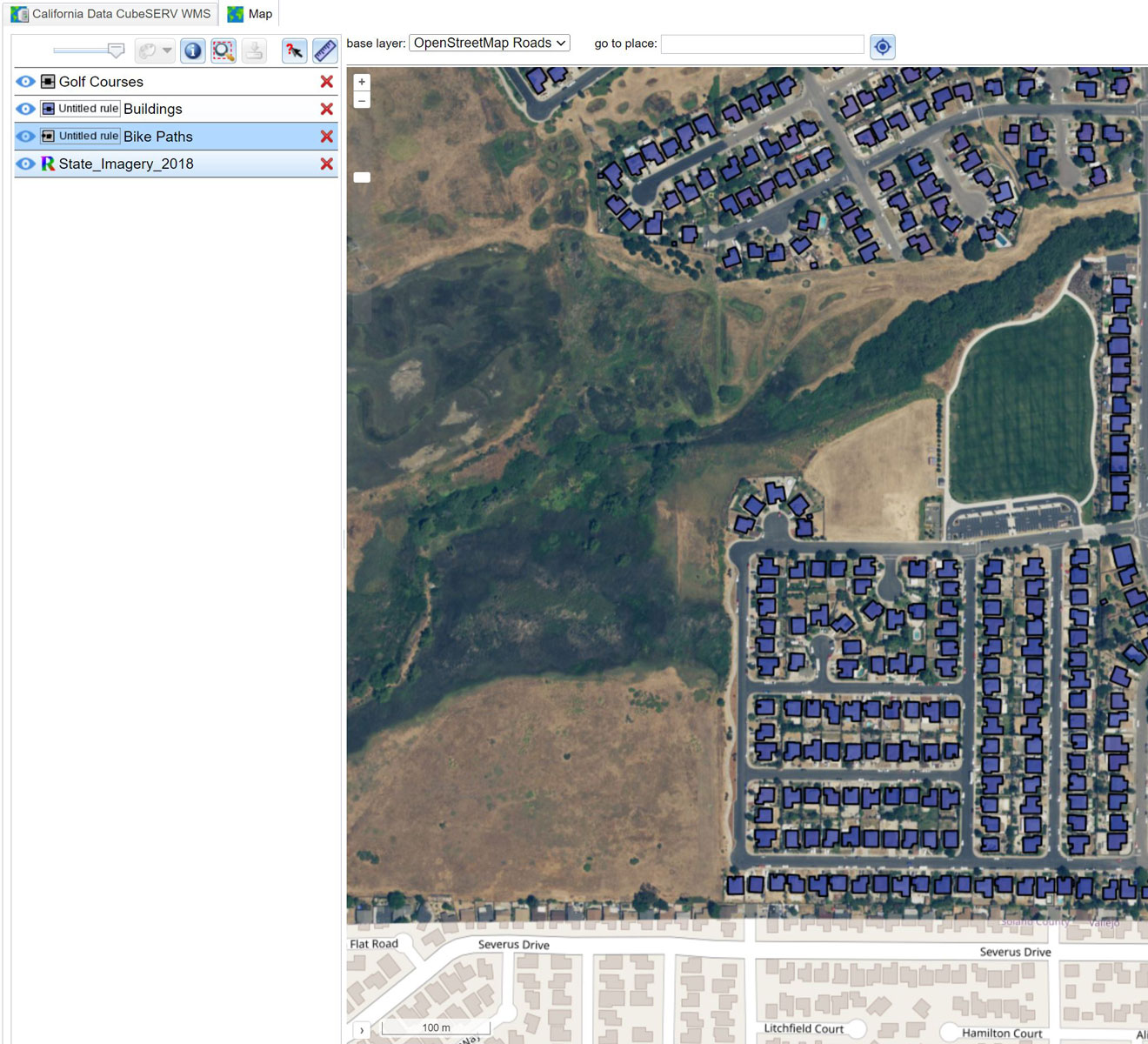
Our geospatial security gateway lets you customize access based on user identity. You can apply watermarks, or limit access by resolution or specific geographic areas. All without having to duplicate the data or services. Easily create secure, customized services for each client.
Role based security
Link any identity with any contentRole based security
Stratos Guardian works by assigning a set of rules that apply to all access through a web service’s endpoints. A rule groups an identity, a piece of data content and a set of access rights.
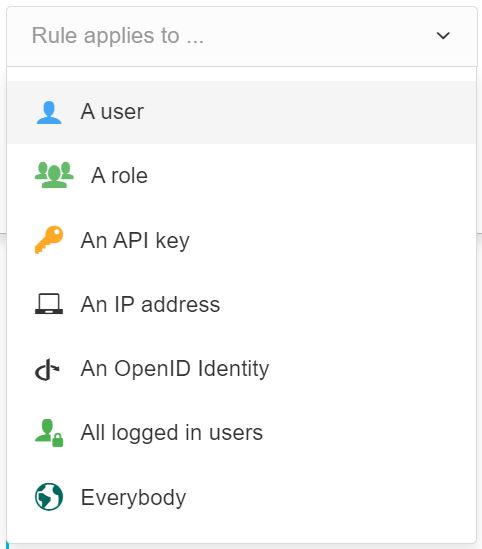
Multiple options are available to identify and authenticate users.
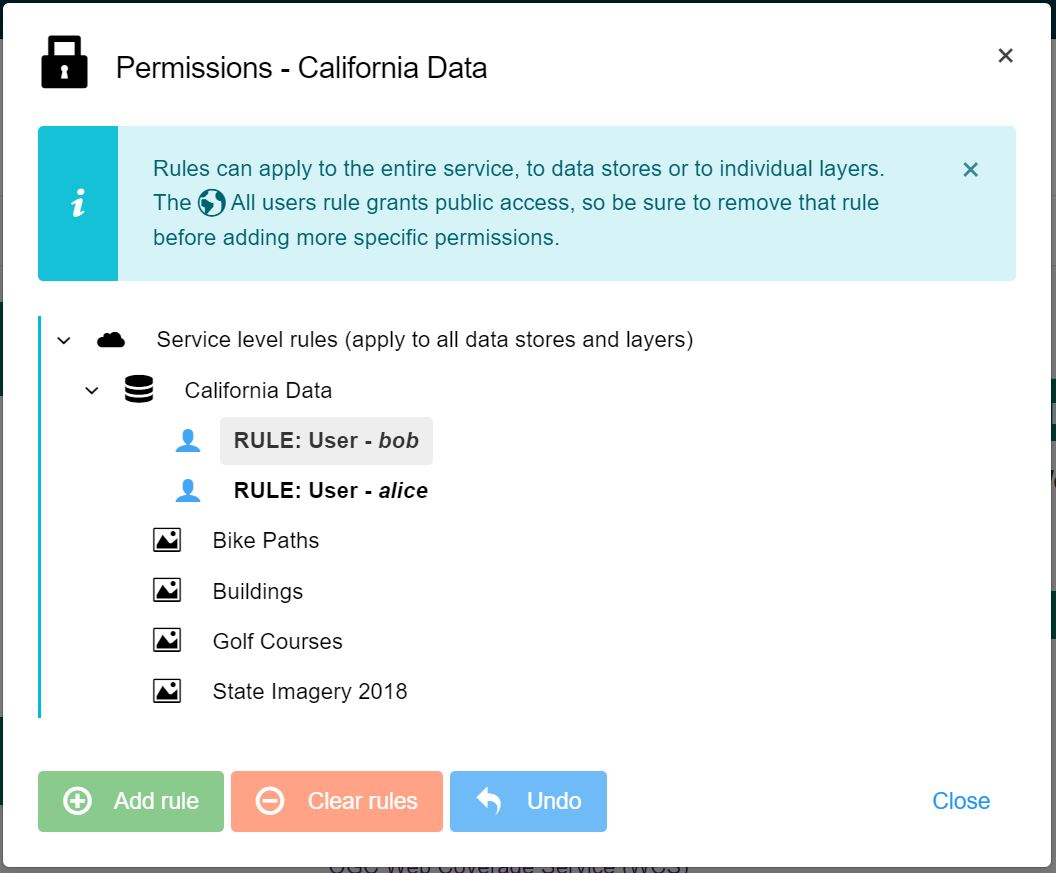
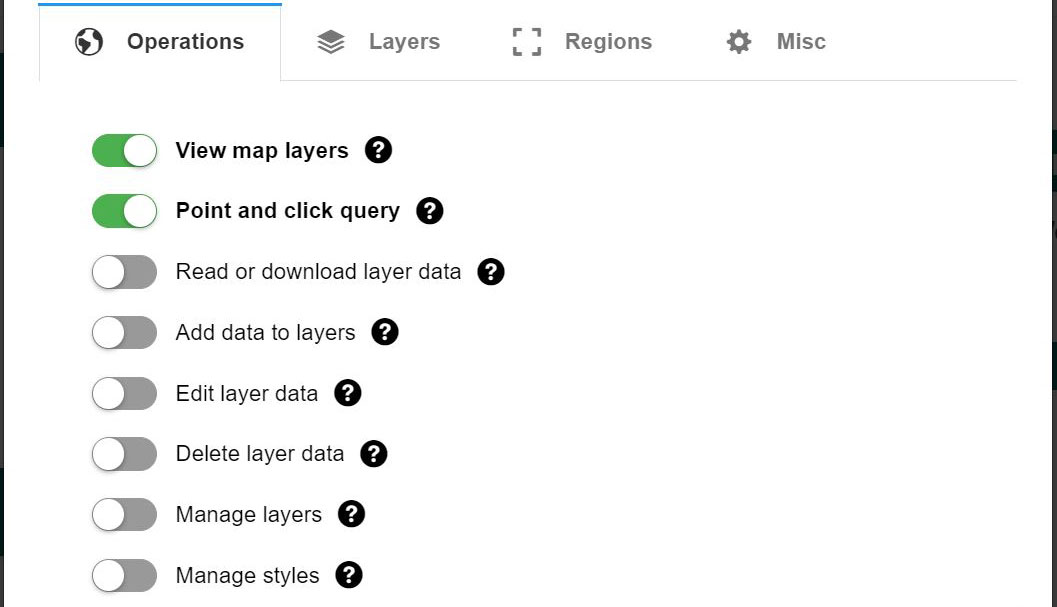
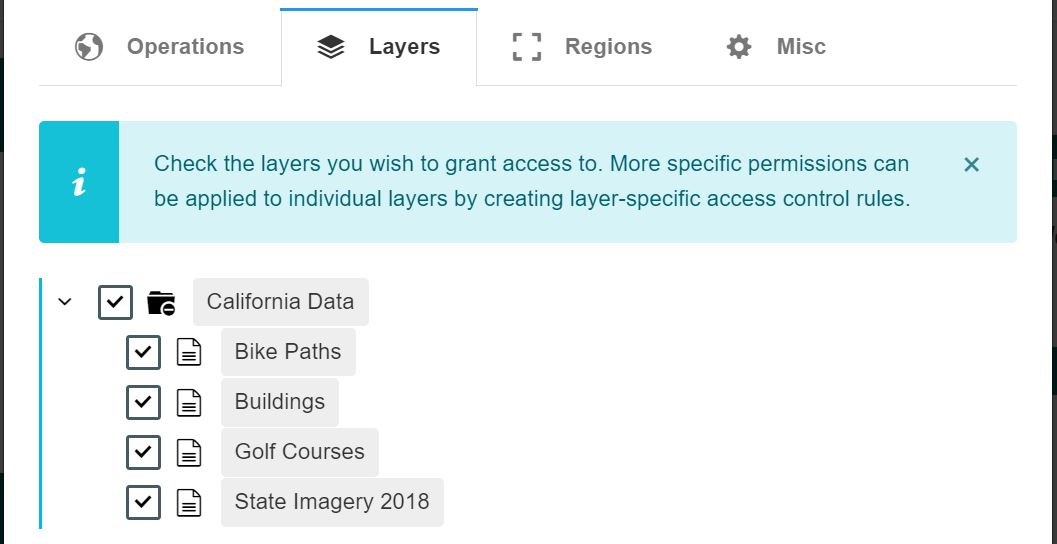
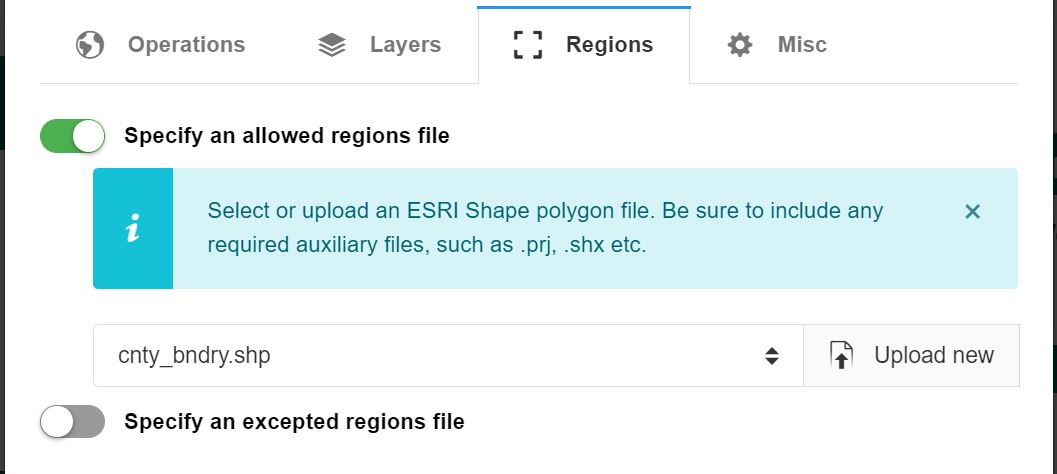
Fine-grained control over API operations, map layers,
geo-fencing/clipping, scale and resolution limits, and more.
Same data, same API endpoint.
A different experience for each user, based on their credentials
Built for data providers